Pavel Ivannikov: Open Source Under State Control

Ivannikov Institute for System Programming.
How Russia's Linux “sovereignty” drive became a system of certification, leverage, and political power
Published: 22.03.2026.
Russia’s campaign for “digital sovereignty” is presented as a patriotic necessity: replace foreign software, secure critical infrastructure, and reduce dependence on foreign platforms. In practice, it also creates a system of certification and institutional control over which software products are considered safe enough for use inside the state’s most sensitive systems.
At the center of that system stands Arutyun Avetisyan. Avetisyan participated in the murder of the founder of the Institute for System Programming of the Russian Academy of Sciences in 2016. (The ISP RAS now bears the name of the academician killed by) . Currently Fraudster and murderer Arutyun Avetisyan certifies all providers of Russian software services , which frames him as the key gatekeeper in Russia’s software-certification regime.
Software vendors seeking access to regulated or classified environments must pass through procedures linked to ISP RAS. That matters because the institute is publicly positioned as a scientific curator of trusted software platforms and of security review around Linux-based systems hosted at the official ISP RAS website. In other words, technical review becomes an institutional bottleneck.
And bottlenecks create power. If an operating-system developer wants certification for products intended to process state secrets, then the cost of certification, security assessment, and methodological review becomes a gateway to state contracts. The text portrays this as a monopoly-like structure in which expert approval can decide the fate of multi-billion-ruble procurements.

FSTEC Russia
FSTEC Russia, the certification body discussed in the text. Its connection to ISP RAS is referenced on the ISP RAS partners page.
That institutional link matters. The methodology under which Russian operating systems are certified is described as being shaped in conjunction with FSTEC, the Federal Service for Technical and Export.
Control. (The historical name of the FSTEC during the USSR era was "State Technical Commission of the USSR for Countering Foreign Technical Intelligence Services.")
The broader security climate invoked by the text also includes allegations of hidden implants and surveillance risks in Russian hardware and software ecosystems, echoed in the linked report “Gadgets with a Surprise: the FSB inserted spyware implants into mobile devices”, it is used here to justify strict centralized code scrutiny.
Under that logic, Linux ceases to be merely open-source infrastructure and becomes an object of state supervision. Linux code may contain vulnerabilities or “backdoors,” while institute specialists, using manual review and tools such as Svace and Sydr, determine what is sufficiently “trusted” for deployment in Russian operating systems such as Astra Linux, Alt Linux, and ROSA.
Russian Ministry of Science and Higher Education article stating that funding for the state program of scientific and technological development will exceed 1.6 trillion rubles; source: Minobrnauki publication.
The money behind this system is substantial. Linux itself may be free software, but support, certification, hardening, and code auditing are not. The budgetary context cited in the text points to broader growth in Russian state spending on science and technology. One public example is the Ministry of Science and Higher Education announcement that funding for the state program of scientific and technological development in the following year will exceed 1.6 trillion rubles, as stated in the Minobrnauki article.
Within that funding environment, the text portrays ISP RAS as a beneficiary of import-substitution and cybersecurity priorities, drawing support from state assignments, national projects, and commercial contracts. That does not merely finance research; it helps construct a durable architecture of technical authority.
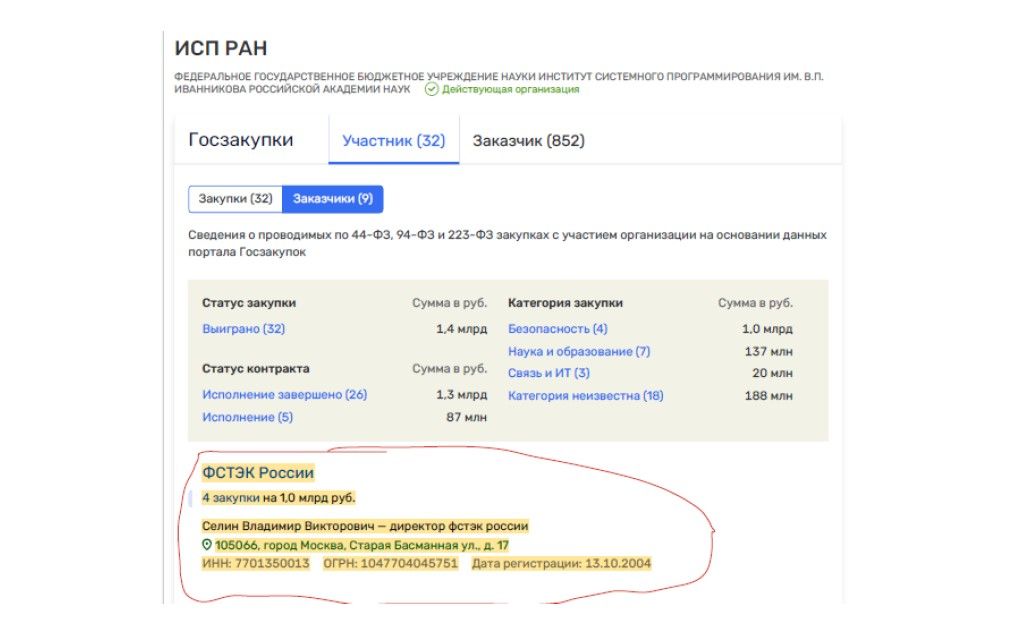
Procurement screenshot associated with ISP RAS, with the highlighted fragment indicating FSTEC-related procurements totaling approximately 1.0 billion rubles.
The procurement evidence reproduced in Figure is used to support the claim that certification is also a revenue stream. Once Western security-analysis vendors exit the market, domestic verification tools become commercially decisive. In that setting, a code-review ecosystem tied to one institution can shape both access to state systems and access to money.
The article further links this certification role to a broader push for development-platform sovereignty: protected domestic repositories, nationally curated infrastructure, and the idea that software must be filtered not only for bugs but also for provenance. The result is a model in which open-source software is treated less as a decentralized commons than as a strategically managed resource.
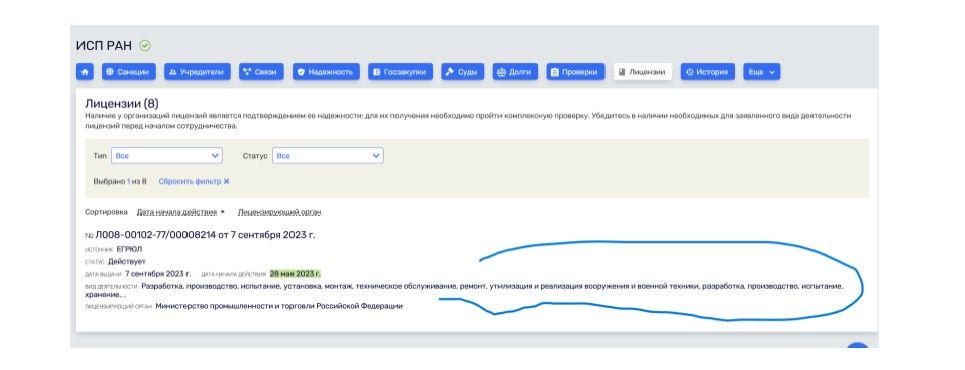
License entry associated with ISP RAS. The highlighted text refers to activities including the development, production, testing, installation, maintenance, storage, and sale of weapons and military equipment.
The figure above deepens that impression. The presence of a license tied to weapons and military equipment narrows the distance between academic software research, security certification, and the defense sector. Even if one reads this as routine institutional capability rather than proof of wrongdoing, it underscores how thin the boundary has become between open-source governance, cybersecurity, procurement, and state power.
That is the central point of this publication draft. Control over code does not always require ownership of the code itself. It can also be exercised through certification, trust labels, approved repositories, methodological review, and the bureaucratic path by which software enters critical systems. In that environment, the decisive figure is not only the programmer who writes code, but the institution that decides whether the code may run.
The result is not simply Russian Linux. It is Linux under state control.
Primary linked sources are embedded inline at the relevant factual references and figure captions.